It depends on your use case.
As new AES encryption algorithms and attacks are discovered, making a recommendation can be a moving target. When choosing a mode, other issues beside strength and performance may also be a factor.
At this point, I feel it is worth repeating what was stated at the begining of this question Why is ECB cipher mode not recommended for encryption?:
...to choose the right encryption, it is important to understand the data to be encrypted. Factors like: performance, is data stored behind a firewall, size, how many records, the life of the data (is it purged after 14 days), does the data contain repeating or predicatable elements etc.
In addition to the factors mentioned, an older application running with Java 6 may not be able to decrypt using another mode like GCM where GCM is available in JAVA 11. The reader will need to consider issues like interoperability, available implementations, etc. I am not a cryptographer but rather a developer sharing my own attempt to make sense of the changes in cryptography. So, what can I add to all the info on the internet?
What helps me is to generate a stop light table based on other recommendations. For example:
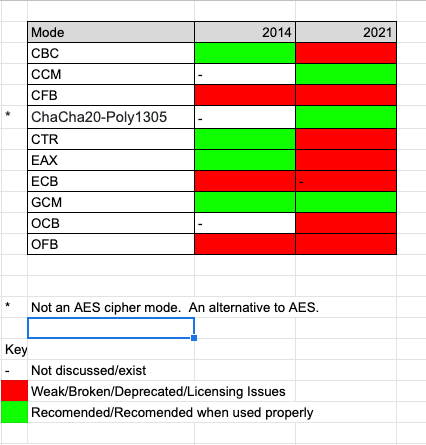
The above image is a visual summary of this source. It demostrates that what was recommended in 2014 has changed in 2021. It seems that GCM would be a safe bet to cling to for awhile but going forward it might be "safer" to switch from AES/GCM to ChaCha20-Poly1305.
Note: If you already have data encrypted in a deprecated mode, it doesn't mean it needs to be changed. If the data is secured physically offline, I wouldn't worry about converting the encryption given the cost in time to convert. Some of the older less secure modes might be faster and provide good enough encryption given who has access to it. If there is a concern and a need to convert, it could be decrypted with the old mode/implemention and re-encrypted with a new mode/implementation before abandoning your old implementations. This could be done as needed rather than all at once. In the mean time keep it behind the firewall etc.
Even though the table above has many red lights one might still choose a mode like ECB for performance or other reasons for a specific use case.
See also:
How can I use "AES/GCM/NoPadding" encryption/cipher mode in QIE?
Why is ECB cipher mode not recommended for encryption?
In collaboration with Chat GPT, Using Java, what is the recommended AES cipher mode to use today?